Psiphon:
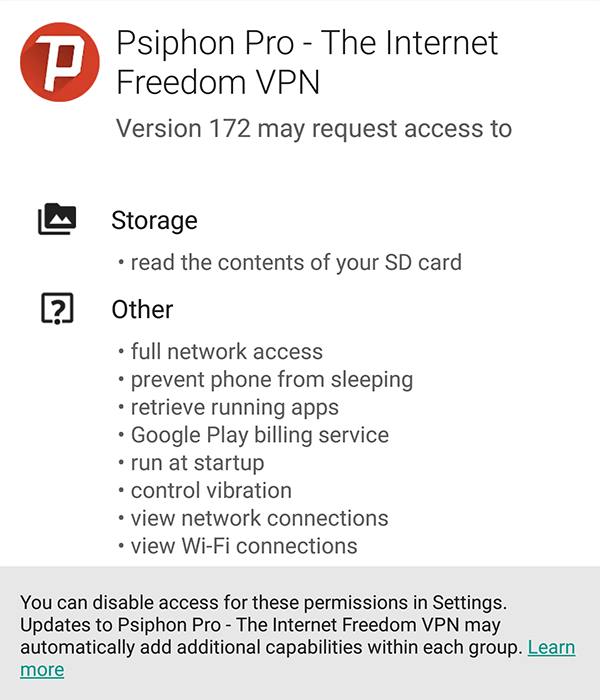
Psiphon is an open source circumvention application that lets users from anywhere in the world access sites that they want to visit.
Consisting of a centrally managed, geographically diverse network of thousands of proxy servers, Psiphon has allowed millions of users from over 200 countries to access content that may be inaccessible in certain regions of the world.
You can find Psiphon on Windows, iOS, and Android
What is Psiphon and Why is it Different than a Traditional VPN:
When a user connects to the network, Psiphon provides a secure "one hop" architecture system, with secure link encryption between clients and servers, with most of the network infrastructure being hosted with cloud providers.
Standard VPNs use a limited number of protocols to connect to a finite number of managed servers. The protocols are usually fixed in how they can be implemented, and as such can be blocked at the network gateway level. The servers, usually operating on fixed IP addresses, can be easily enumerated and thus blocked.
Psiphon operates over many protocols, connecting to a fast-moving network of servers in the cloud. We constantly change the way we handle these connections, making sure you are able to access the content you want at all times.
Psiphon Respects User Privacy:
When you use Psiphon, we hide your IP address as soon as you connect - and we don’t store it anywhere. We have no user accounts so do not collect or store any account access information. Any data that is stored on a user is in aggregate, with no individual personally identifying information.
Psiphon is not explicitly designed to ensure the integrity of your traffic over the Internet. But, in the case where a censor is intercepting your SSL/TLS traffic using compromised Certificate Authority (CA) keys, or if they have installed their own root CA certificates on your computer or device, Psiphon can help.
Psiphon’s server authentication scheme also does not rely on the commercial CA system, so you can be reassured that Psiphon will always connect you to servers that are managed by Psiphon Inc.
Psiphon employs a multitude of obfuscation techniques designed to bypass Deep Packet Inspection (DPI) fingerprinting firewalls. Psiphon tunnels through firewalls using a transport protocol based on obfuscated SSH (a fully random-looking protocol over the wire); using HTTP and HTTPS protocols; and by connecting through Content Delivery Networks (CDNs) and network data centers around the world.
Find out more about Psiphon’s security measures from an independent security assessment here